Latest News
For the latest news and ASX announcements Click here




Our team is standing by to ensure maximum uptime and satisfaction for you and your end-users. All support enquiries submitted via the form below will have a ticket generated automatically. If the request is mission critical, feel free to give us a call. Partners and optional end-users enjoy 24 hour support.
Jump to section:
Cloud FAQ General FAQ Networking FAQFill in the form and a support ticket will be generated by our system. Once this is assigned, you will receive an email notification with the ticket number and one of our team will be in contact to resolve your ticket as soon as possible.
It helps to resolve the issue quickly if you can provide as much information as possible such as software name, situation which caused the error, steps you took and even any error codes or messages would be helpful.

We've partnered with DC Two for nearly ten years, and love their friendly approach to looking after their clients. DC Two are always happy to help when something needs quick attention. They've even helped pitch a few solutions to our end clients as well!
Top marks to the DC Two team and we'll continue partnering with them for many years to come.
- Steve Edwards, activIT Systems
Cloud computing is a marketing term for technologies that provide computation, software, data access, and storage services that do not require end-user knowledge of the physical location and configuration of the system that delivers the services. A parallel to this concept can be drawn with the electricity grid, wherein end-users consume power without needing to understand the component devices or infrastructure required to provide the service.
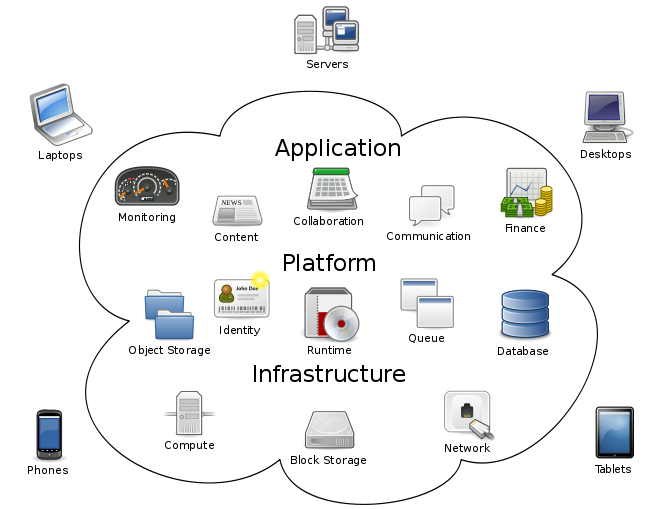
Cloud computing describes a new supplement, consumption, and delivery model for IT services based on Internet protocols, and it typically involves provisioning of dynamically scalable and often virtualised resources. It is a byproduct and consequence of the ease-of-access to remote computing sites provided by the Internet. This may take the form of web-based tools or applications that users can access and use through a web browser as if the programs were installed locally on their own computers.
Cloud computing providers deliver applications and services via the internet, which are accessed from web browsers and desktop and mobile apps, while the business software and data are stored on servers at a remote location. In some cases, legacy applications are delivered via a screen-sharing technology, while the computing resources are consolidated at a remote data center location.
At the foundation of cloud computing is the broader concept of infrastructure convergence (or Converged Infrastructure) and shared services. This type of data centre environment allows enterprises to get their applications up and running faster, with easier manageability and less maintenance, and enables IT to more rapidly adjust IT resources (such as servers, storage, and networking) to meet fluctuating and unpredictable business demand.
Most cloud computing infrastructures consist of services delivered through shared data-centres and appearing as a single point of access for consumers' computing needs. Commercial offerings may be required to meet service-level agreements (SLAs), but specific terms are less often negotiated by smaller companies.
The tremendous impact of cloud computing on business has prompted the federal United States government to look to the cloud as a means to reorganize their IT infrastructure and decrease their spending budgets. With the advent of the top government official mandating cloud adoption, many agencies already have at least one or more cloud systems online.
Some very good examples of Cloud Computing are Salesforce, Google Docs, Skydrive, Dropbox, Hotmail, Zoho Office, Xero plus many more.
Virtualisation is the creation of a virtual (rather than actual) version of something, such as an operating system, a server, a storage device or network resources.
Virtualisation allows multiple operating system instances to run concurrently on a single computer and by inserting (or installing) a virtualisation layer (or a Hypervisor) on the computer hardware you can effectively separate the hardware from each individual single operating system as per the below diagram.
A Virtual Data Centre (using virtualisation) is a data centre which is created 'Virtually', effectively in memory, on an existing shared computing platform which would be housed, or located within a 'Physical Data Centre'.
The Virtual data centre provider will have several very high performance and high capacity 'physical servers' and in a 'virtual' fashion, segregate and divide the total resources of the physical platform to serve many Virtual Data Centres or Virtual Servers.
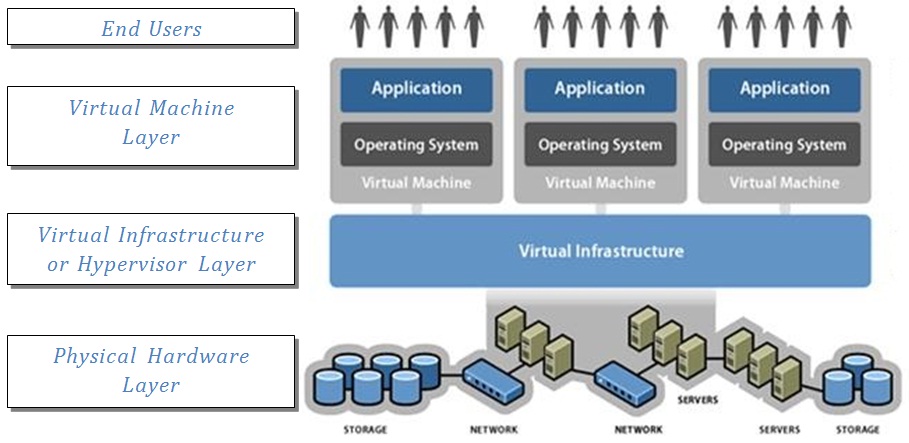
This diagram is a simplified representation of what the layers of the Virtual Data Centre are.
Physical Layer - is the physical server, networking equipment and routers and hard disk storage devices
Hypervisor Layer - is effectively the operating system which controls the physical hardware and is the 'container' which allows multiple 'virtual machines' or 'virtual servers' to operate on top of a single physical server. The Hypervisor controls the sharing of all physical resources such as memory and processing and ensures all of the 'guest hosts' (hosted virtual machines) co-exist and 'play nicely together' on the same physical hardware.
Virtual Machine Layer - is what we currently know as the operating system and applications that make up either a server or computer. A good example of a server virtual Machine (VM) would be a Windows Server running Exchange which combined acts as an email and collaboration server, or, the VM could run Windows 7 with Microsoft Office and this could be a user's desktop machine.
End Users - the end users of the VM could be you or me when we check our email, or type a letter or watch a YouTube video or do whatever else it is that we do as IT consumers. The end user function could also be that of a simple off site backup for all of our important data.
As a simple example, let's say you buy a physical server from IBM and ensure it is configured with as much memory and processing power as you can get in it. Let's say you have 100 Gigabytes of memory. Onto that server you could very easily load 10 x Exchange email servers as described above while simultaneously running over 60 x Windows 7 desktop machines for end users.
Cloud Computing, when compared to an on-premise deployment, in most cases, can end up being less expensive and more valuable.
Cloud Computing however does not come free, there are costs, but it would be expected that any savings made by moving workloads to the cloud would outway any additional incremental costs incurred by moving to the cloud.
What are the items that you will need to consider for a like-to-like comparison?
We undertook a very comprehensive ICT Architecture Scoping Study for a health service that will be operating across 12 sites with over 230 staff across some of the most remote areas of Australia. The study required us to compare three complete deployment options including full cost comparisons for each over a 36 month period.
Some of the results along the way actually surprised us but the outcome was not surprising with the Private Cloud solution working out about 8% less over 3 years than the next closest option.
A public cloud is one based on the standard cloud computing model, in which a service provider makes resources, such as applications and storage, available to the general public over the Internet. Public cloud services may be free or offered on a pay-per-usage model.
Community cloud shares infrastructure between several organizations from a specific community with common concerns (security, compliance, jurisdiction, etc.), whether managed internally or by a third-party and hosted internally or externally. The costs are spread over fewer users than a public cloud (but more than a private cloud), so only some of the benefits of cloud computing are realised.
Hybrid cloud is a composition of two or more clouds (private, community, or public) that remain unique entities but are bound together, offering the benefits of multiple deployment models. It can also be defined as multiple cloud systems that are connected in a way that allows programs and data to be moved easily from one deployment system to another.
Private cloud is infrastructure operated solely for a single organization, whether managed internally or by a third-party and hosted internally or externally.
Private clouds have attracted criticism because users "still have to buy, build, and manage them" and thus do not benefit from lower up-front capital costs and less hands-on management, essentially "lacking the economic model that makes cloud computing such an intriguing concept".
The irony of cloud computing is that contrary to it's name, every cloud must exist on the ground, in a data centre somewhere!
Just as Cloud Computing is the much publicised marketing phrase for the next genration of hosted applications, the key distinction between Cloud computing and traditional computing is that a cloud environment is virtual and elastic.
For consumers, a properly designed and executed 'Virtual Data Centre' offers the virtualisation capability for Cloud just as the same should be able to offer the flexibility and adaptability to ensure that the Virtual Data Centre also has the elastic properties to allow consumers to scale up resources as demand warrants, just as easily as scaling down resources when demand wains.
A great example of this elasticity would be an accounting firm requiring more processing power at the end of the financial year to perhaps process end of financial year accounts for clients or the christmas period for retailers requiring handling many more transactions.
When a business wishes to utilise the services of a Virtual Data Centre (or VPS) provider, they should be presented with a 'menu' of choice with the below as the key options;
See our MyDaaS product website for full information.
Many companies have turned to virtualization technologies for their servers in their data centres to simplify administration and to reduce management chores and operating costs while maintaining reliability and safeguarding against disasters. Seeing the significant benefits virtualization delivers in those environments, companies are now looking to apply the same technology to their desktop computers.
The idea behind what is called a Virtual Desktop Infrastructure (VDI) is to run desktop operating systems and applications inside virtual machines that reside on servers in the data centre. Desktop operating systems inside virtual machines are also referred to as virtual desktops. Users access the virtual desktops and applications from a desktop PC client or thin client using a remote display protocol (RDP) such as Microsoft's RDP, VMware View's PCoIP, or even a Citrix technology and get almost the full features as if the applications were loaded on their local systems, with the difference being that the applications are centrally housed, hosted and managed.
Similar to server virtualization, VDI offers many benefits. Specifically, desktop administrative and management tasks are significantly reduced; applications can quickly be added, deleted, upgraded, and patched; security is centralised; and data is easier to safeguard and back up.
In today's work environment, where workers can be in geographically dispersed, remote offices, the data stored on distributed desktop computers is often vital to the operation of the business. Such data could include correspondence and documentation that would be essential in protecting intellectual property. Or the data could be essential corporate records, files, or data.
Regardless of what the data is, there is generally a need to protect it from corruption and it must be backed up in case of a hard disk crash, user error, or malicious destruction.
To enable the proper design and deployment of Microsoft Windows Virtual Desktops (VDI) environments, we will need to consult with the business users to ensure that the correct hardware platforms and Microsoft licensing is deployed which will optimise costs and increase ROI.
A Virtual Server is a server that shares computer resources with other virtual servers. In this context, the virtual part simply means that it is not a dedicated server -- that is, the entire computer is not dedicated to running that individual server's software.
Virtual Servers are a very popular way of providing cost effective hosting services. Instead of requiring a separate physical computer for each server, dozens of virtual servers can co-reside on the same physical computer. In most cases, performance is not affected and each virtual server behaves as if it is being served by it's own dedicated physical server. However, if too many virtual servers reside on the same physical computer, or if one virtual server is allowed to hog resources, the other virtual servers on the same physical server could operate more slowly.
To ensure performance on the DC2 Platform, every Virtual Server or Virtual Data Centre is restricted to a maximum amount of resources to ensure that no individual Virtual Server or Virtual Data Centre can hog more resources than they are allowed.
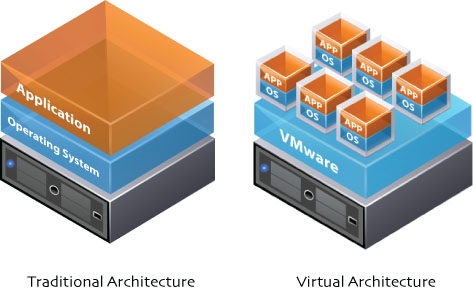
The diagram shows you the logical difference between a traditional Physical Server deployment and Virtual Server architecture with the VMware layer installed between the physical computer and the Operating System (OS) and Application (Apps) layer. VMware controls, shares and allocates the physical resources amongst all of the Virtual Servers and ensures that they all work together properly.
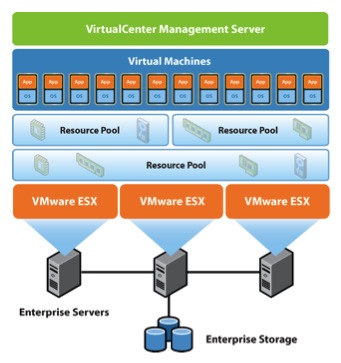
As an extension from the Virtual Server, Virtual Data Centres are best described as a dedicated set of resources (or a Resource Pool) on the host Physical Servers.
The maximum (and reserved) resources of the Resource Pool are defined in VMware and the individual Virtual Machines are pooled together in groups to be managed together.
Virtual Data Centres are a great way for organisations requiring larger amounts of resources to deploy and manage those resources.
In the diagram, you can also see that Resource Pools can be 'nested' inside each other. Nesting Resource Pools can make it easy for larger organisations to allocate and divide the Parent Virtual Data Centre, or Parent Resource Pool, into further 'child' resource pools suitable for departments, or sections within the main business.
DC Two utilises a variety of enterprise grade hardware and equipment including servers from IBM, Lenovo and Super Micro, Storage from vendors such as IBM, Lenovo, Samsung, VMware and DataCore and Networking from the likes of Cisco, Juniper, IBM and Fibrestore.
DC2 select the most appropriate hardware which enables us to deliver high availability and energy efficiency for intense virtualised commercial environments like eBusiness/eCommerce, collaboration, virtualisation, database and enterprise resource planning applications.
There are many enterprise applications which have very specific hardware requirements and this is why DC Two has deployed specific hardware clusters which support the highest performance and compatibility for Microsoft SQL Server, SAP ERP, SAP HANA and VMware Horizon View.
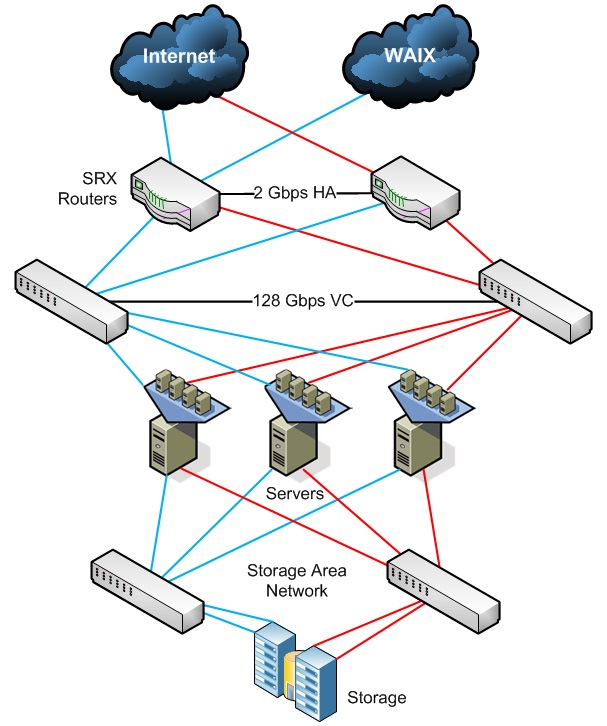
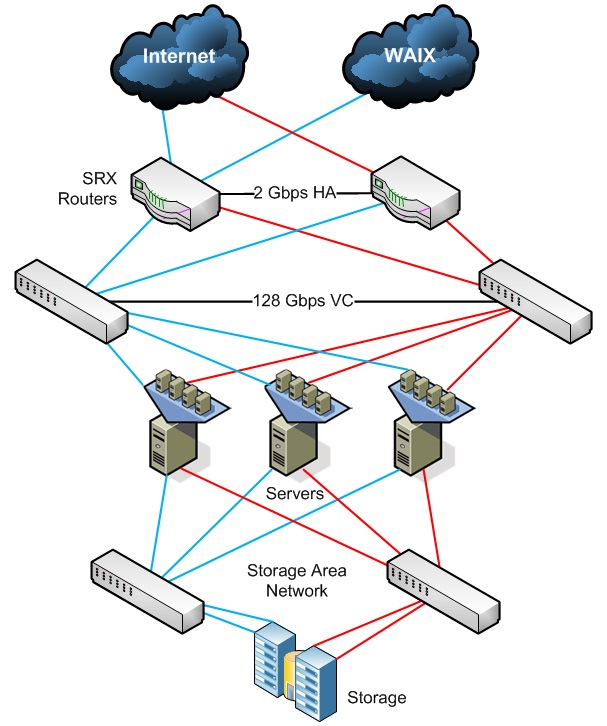
This diagram is a network layout showing the High Availability design of each of the virtual platform nodes operated by DC Two.
Definition: Backend as a Service. Providing web and mobile app developers with a way to link applications to cloud storage and API communication, while still maintaining features like user management, notifications and other integrations.
Definition: Desktop as a Service. Providing a virtualised hosted computer desktop, which is just like your regular desktop computer as it includes an operating system, software and all your files. But it can be accessed remotely using a client such as VMWare Horizon from any computer or device. Main benefit being that there is no hardware to maintain and features can be quickly modified as the need changes. Check out our great business grade cloud desktops.
Definition: Disaster Recovery as a Service. Providing a fully hosted and automated backup solution enabled by your offsite back up, allowing you to quickly recover and keep working. Check out our comprehensive backup and disaster recovery solution.
Definition: Hardware as a Service. Leasing/rental of computing power and hardware from a central provider. Includes attached managed services so you can save time and money on managing your IT infrastructure. Often includes software, backups and recovery solutions. Our on-premises cloud solution or our managed hosting service are a few ways you can take advantage of this, hosted at your place or in our data center.
Definition: Infrastructure as a Service. Provisioning of a cloud based/ hosted service that enables the hypervisor of choice to support a large number of virtual machines and other systems. Easily scalable to suit high end business requirements, and includes management of usage information for billing etc. Often includes virtual machine images for easy template deployment of new systems quickly as required. See our various cloud solution options.
Definition: Payments as a Service. Connection of two-way communication between payment systems such as banks, credit cards, eWallets and more. Includes systems like SWIFT international transfers and direct debiting. Allows merchants to use a single simplified interface to do local and global payments.
Definition: Platform as a Service (Paas) OR Application Platform as a Service. Providing cloud hosted platform for developers to develop, run and manage applications without having to maintain and back up their own hardware infrastructure. Takes advantage of the redundancies and speeds possible only from a dedicated cloud host provider. We can host pretty much any software application for your business such as accounting software, exchange, SQL server plus more. Check it out here or talk to us about your custom requirements.
Definition: Security as a Service OR Software as a Service. Hosted security and software subscription service. Provides considerable savings to the business as they don't need to purchase on site hardware and the solution is quickly scalable. Includes hosted software solutions like authentication, anti-virus, anti-malware, anti-spyware, intrusion detection, penetration testing plus a lot more. Protects a business from online threats and attacks.
Check out our SaaS options.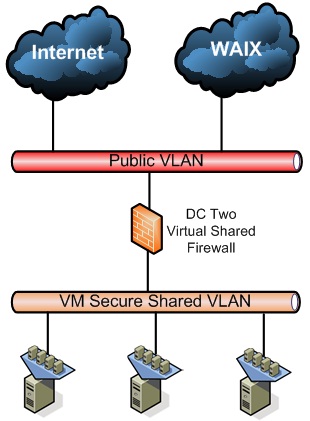
VPS Basic security is the base security level on the DC2 Platform which secures single VPSs in several ways;
VPS Basic Secured VPSs can only connect to external communications via the internet as below;
A Private Cloud VLAN and private DMZ firewall appliance is the next level of security on the DC2 Platform which secures all of your chosen VPSs in a private, dedicated Virtual Local Area Network (VLAN) behind your own private firewall appliance or device;
A Private VLAN and Firewall will provide a great level of security for hosting companies and any deployments needing a good, secure internet hosting solution as shown in the diagram below;
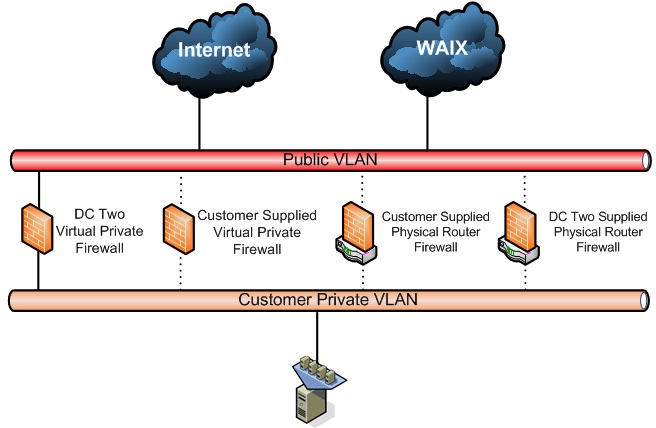
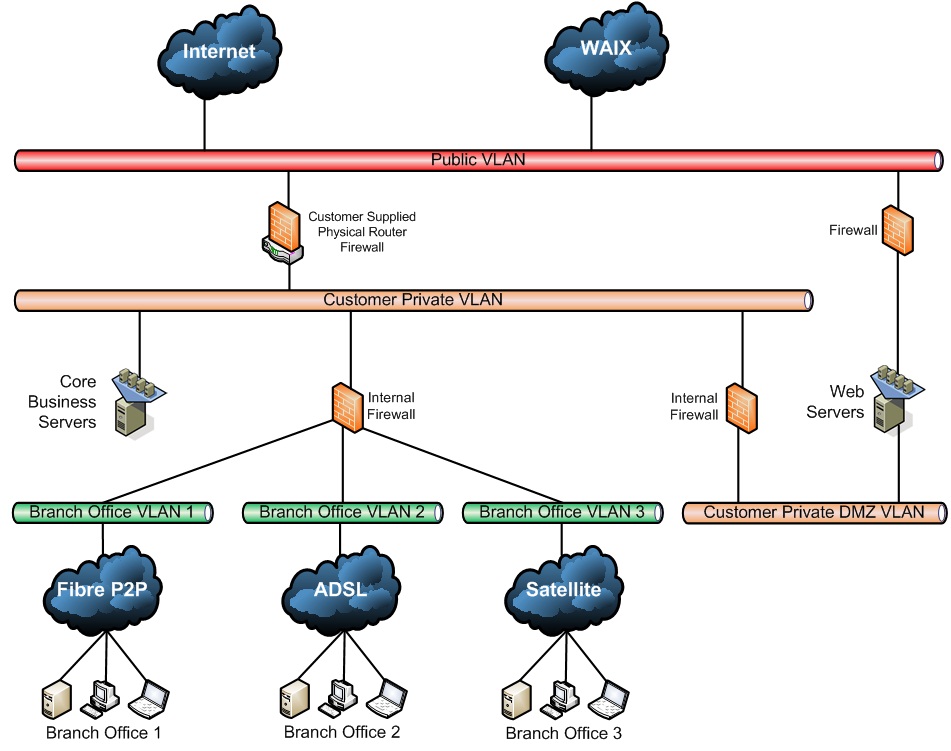
A Private Cloud VLAN with a firewall appliance connected back to your main office via a dedicated Point to Point (Direct Connect) communications connection (fibre, BDSL, ADSL etc) is a great way to connect your business premises to the Cloud.
The Private Cloud VLAN and P2P offers all of the same levels of security as the Private Cloud VLAN option with some extra benefits;
Dedicated Point to Point communications - A dedicated, secure point to point communications link between your site and the data centre can achieve several things;
A Private VLAN with a private DMZ Firewall and a point to point connection is a great way for businesses to step into the cloud as shown in the diagram below;
A completely Private Cloud network is a good solid way for organisations who already have significant deployments based either at another site, or perhaps on-premise to increase IT compute or storage capacity without re-designing their networking infrastructure.
Connecting your existing networks to the DC Two hosting platform can enable your business to hook into the benefits of the cloud without any 'perceived detriments' while taking advantage of the cost and performance benefits of dedicated point to point communications connections.
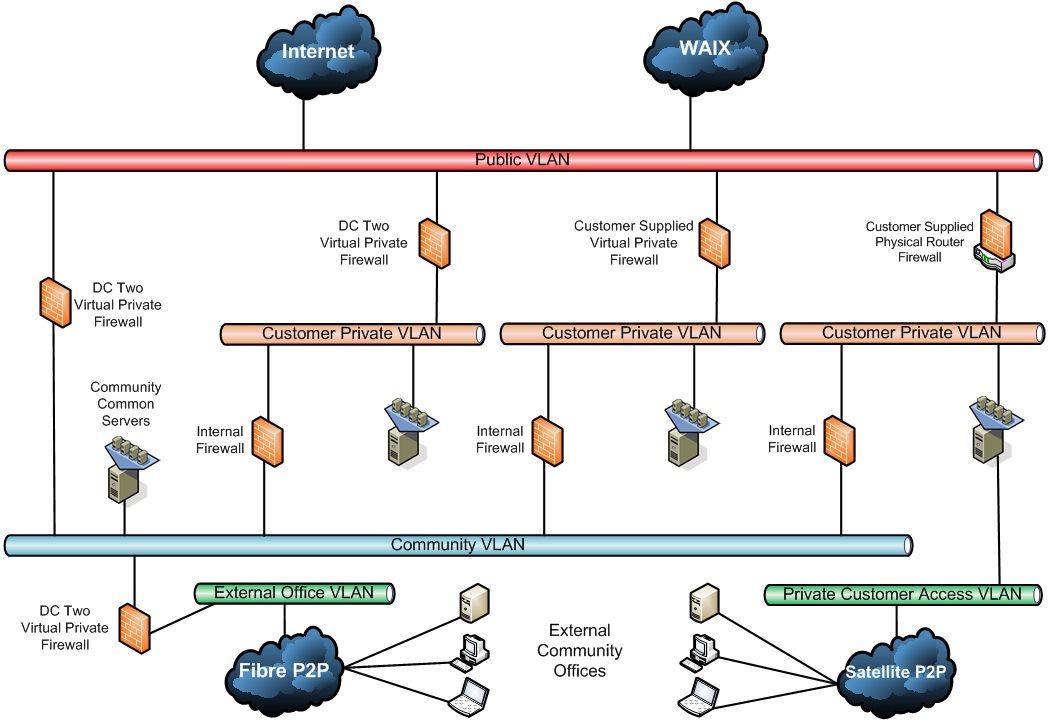
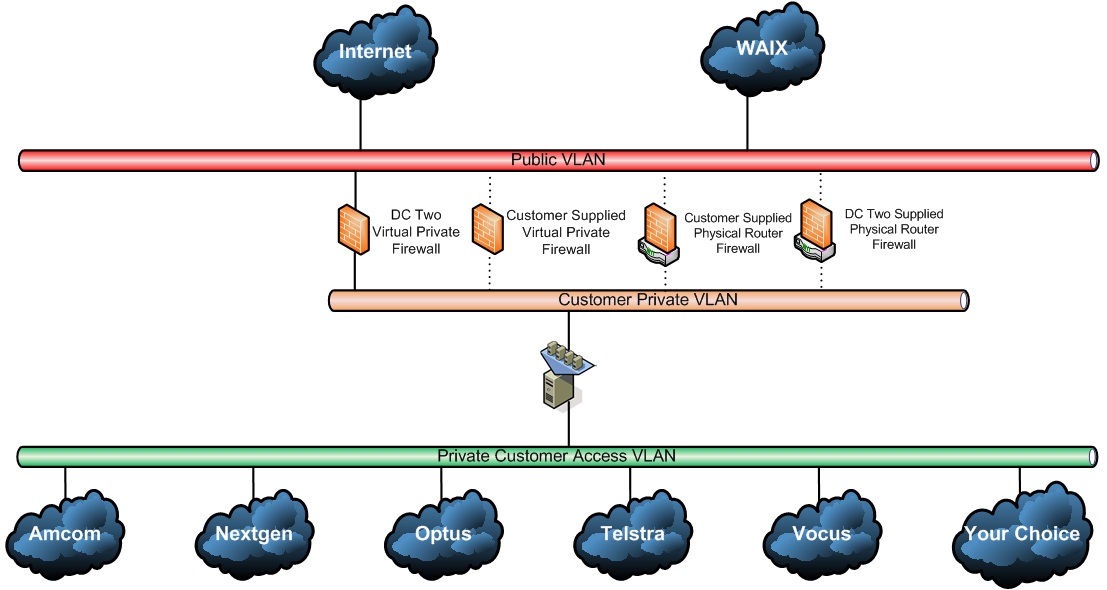
Community Cloud Networks are a great way to share the benefits of the economies of scale that communities can enjoy.
Communities also often share a lot of data and information between each other and joining together and developing a Community Network, this data and information can much more easily be shared.
By mixing and matching the various internet, peering, P2P over a variety of connection types (fibre, BDSL, ADSL, satellite etc), VLANs, firewalls (physical and virtual), virtual servers and/or virtual desktops and many other components, DC Two can assist you to design, implement and operate whatever you require. Please do not hesitate to contact our team to help you put together whatever it is you are thinking of.
The below diagram is a good example of a Community Cloud that DC Two engineers designed for a regional Health Service in Australia.
The DC2 Platform is capable of hosting the most complicated and complex Hybrid Cloud networks and deployments.
By mixing and matching the various internet, peering, P2P over a variety of connection types (fibre, BDSL, ADSL, satellite etc), VLANs, firewalls (physical and virtual), virtual servers and/or virtual desktops and many other components, DC Two can assist you to design, implement and operate whatever you require. Please do not hesitate to contact our team to help you put together whatever it is you are thinking of...
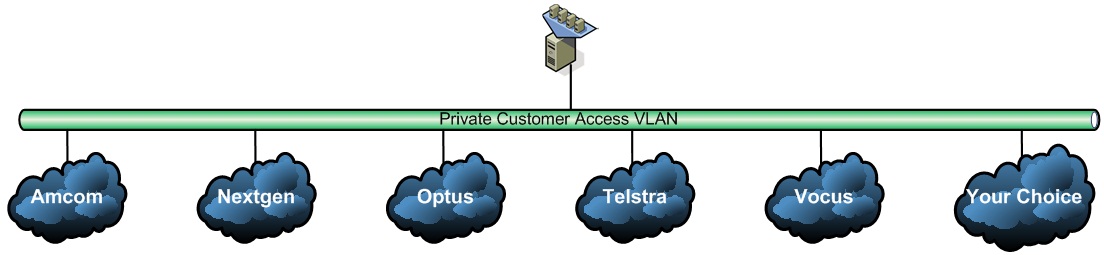
There are several ways you can connect to the DC Two Cloud platform including the below;

DC Two is an ISP (Internet Service Provider) operating our own BGP and DNS with both IPv4 and IPv6 address space for your internet connectivity, however, you also have the choice to bring your own if you so choose.
Unless specifically required, all of our VMs are supplied with private IP address space (RFC 1918) and then port mapped to external IP address space as required.

Depending on your communications and security requirements, you might find connecting a dedicated Point to Point communications service from your head and branch offices directly into the DC2 Platform to be advantageous.
Dedicated connections can be provided by a variety of carriers as listed below using a wide variety of mediums such as fibre optic, mid-band ethernet, ADSL, BDSL, SHDSL, ethernet, satellite and microwave.

Wherever we can, we connect our network with local 'peers' so we can share internet traffic with other network operators which can achieve several key things for our cutsomers inclduing lowering internet latency, increasing connection speeds and bandwidth all while lowering overall costs for those operators who 'peer' with each other.
If required, we can provide a 'Peer Connect' network ONLY connection which enables us to 'lock' your traffic to a specific network path which enables us to 'lock' in your traffic pricing at much lower prices which is very beneficial for off-site backup and cloud storage solutions in particular which both require lots of bandwidth to function efficiently.

DC Two have a direct secure network connection into the Satcomms satellite network.
SatComms owns and operates it's own Earth Station (teleport) in Henderson, Western Australia. From this location, SatComms is able to Connect to global telecommunications partners, delivering customers' data & voice traffic with the level of security and performance required. The SatComms Teleport hosts customers' equipment and links remote sites to fibre and PSTN networks. This site also delivers Engineering & Support, along with the management of all customer networks end-to-end within the Network Operations Centre.
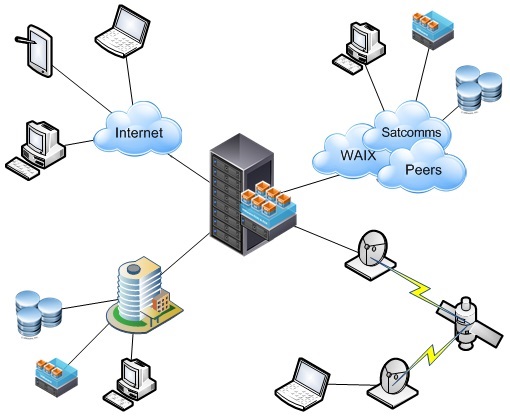
As you can see from the diagram below, it is also very simple for us to provide you with a Combination Connect to either some or all of the connection types of Internet, Direct, Peer or Sat, effectively allowing you to optimise all of your connections for both performance and price.
The DC Two network is flexible enough for you to have as many incoming network points as your network and deployment requires.
Perth CBD - AAPT/TPG, Optus, Vocus (Amcom), IX Australia (WAIX)
Osborne Park Carriers - Vocus/Amcom. Telstra, AAPT/TPG
Speedcast Satellite Teleport AMC Henderson - Satcomms, Inmarsat, Iridium - for more information, please see www.speedcast.com
Secure Data Centre Darwin - Vocus, Chan DC - Direct Point to Point Connectivity for NT Gov. departments and organisations
The DC Two Network, Security and Access (or NSA) virtual Appliance has been developed by DC Two as a result of our need to be able to combine, control and supply several services across our network and systems to our customers.
DC Two have implemented the Juniper SRX Series Services Gateway devices which offer a high performance security, routing and network solution for enterprise and service providers. SRX gateways pack high port density, advanced security, and flexible connectivity, into a single, easily managed platform that supports fast, secure, and highly available data centre operations.
DC Two utilise both the hardware firewall functionality of the Juniper SRX Series Services Gateway devices and the virtual appliance software capabilities of our own custom built Hardened DMZ/Firewall appliance.
For switching DC Two have deployed Juniper's EX Series Ethernet Switches which address the access, aggregation, and core layer switching requirements of data centre environments, providing a foundation for the fast, secure and reliable delivery of applications that support strategic business processes. EX Series enterprise Ethernet switches deliver operational efficiency, business continuity, and agility.
In the data centre, the EX Series Ethernet switches are well suited to meeting the challenges of server virtualization and distributed applications. By implementing Juniper's 3-2-1 data centre architecture, the EX Series Ethernet switches enable enterprises to not only improve performance but also to increase operational efficiency.
The SRX Series Service Gateways and EX Series Ethernet Switches are based on Junos, Juniper's proven operating system which delivers security and advanced protection services, the foundation of the world's largest networks. Junos also supports rich routing and switching capabilities, and Junos' unique architecture provides reliable service operations and manageability, even under the highest loads.
The below is a network diagram showing the High Availability design of each of the virtual platform nodes operated by DC Two.
The security of the DC2 Platform itself consist of many layers to ensure the ultimate protection for your Virtual deployments and includes the following features;
A Firewall is a device designed to permit or deny network transmissions based upon a set of rules and DC Two uses both hardware Juniper SRX firewall/security devices and hardened Linux virtual Firewall Appliances to secure our networks.
DC Two has deployed an Active Intrusion Detection System (IDS) to monitor and secure our networks and systems for malicious activities.
Most network providers have only implemented standard IDS systems whereby they will be notified if there is a problem, but most of the time, by the time you realise there is a problem, it can be too late, whereby with an Active IDS system, the system itself will watch for malicious activities and pro-actively block and engage with the potentially malicious traffic itself.
A Virtual Local Area Network (or VLAN) has the same attributes as a physical Local Area Network (or LAN), but it is configured and run 'in memory' within the networking and communications equipment (switches and routers). A VLAN can also span across multiple switches and communications connections which can allow the VLAN to stretch out to connect remote sites.
VLANs are an ideal and very secure way to divide up network resources to allow multiple customers to share the same physical resources.
To ensure that the various network traffic segments do not interfere with each other, we have divided our internal network up into multiple VLANs. Network segmentation via VLANs keeps all of the network traffic such as SAN storage, internet, management, client data and any other traffic types completely separated from one another and unable to interfere and cause issue between each other.
All of the back end physical management interfaces and ports which control the base functions of physical servers, storage and networking hardware equipment are connected to their own completely separate physical network to ensure maximum security and segmentation and ensure that we always have full unencumbered access to control the entire platform, regardless of external communications.
All of the DC Two systems are monitored and checked every minute of every day by multiple alerting and notification systems to ensure that we can be on-top of any issues pro-actively, before they become a problem.
Virtualisation is the creation of a virtual (rather than actual) version of something, such as an operating system, a server, a storage device or network resources.
In addition to the standard security inclusions, there are also several additional security options which you may wish to deploy or implement depending on your requirements and needs such as;
DC Two provide a managed virtual firewall solution however you may wish to deploy a virtual firewall appliance that you are already using and/or familiar with. The DC Two virtual platform can facilitate just about any OS or virtual appliance but just to be sure, please contact DC Two with your specific enquiry.
Perhaps your preference is to deploy a physical firewall appliance/device rather than virtual. DC Two can host your routers and join them into the DC Two virtual fabric very easily to give you full access and control over your environment.
Trend Micro SecureCloud™ provides data protection for public and private clouds and your VMware vSphere virtual environments. Protect and control your confidential information with this efficient and easy-to-use data encryption service that keeps your data private and helps meet your regulatory compliance requirements.
SecureCloud can be deployed on hosted services or as an on-premise software application. Either way, you the customer, control the encryption keys, not the hosting provider, giving you the freedom to encrypt data in virtual data centers or in the cloud, and even to move data between cloud vendors.
If security is a serious concern for you and the above options still aren't enough, then considering private dedicated server hosts could be your next step.
DC Two would deploy sufficient physical server hosts dedicated just for you and your compute loads with your own managed private VMware environment, managed private Veeam backup environment which will ensure that the only network traffic that enters your hosts is your own traffic.
To take the dedicated hardware to the next level, we can, if required also deploy your own private managed SAN.